Adversarial Attacks
Explore how adversarial attacks manipulate machine learning models. Learn about white-box and black-box strategies, risks to AI safety, and defense with Ultralytics YOLO26.
Adversarial attacks are a sophisticated category of manipulation techniques designed to fool
machine learning (ML) models into making
incorrect predictions with high confidence. These attacks operate by introducing subtle, often imperceptible
perturbations to input data—such as images, audio, or text. While these changes look harmless or random to a human
observer, they exploit specific mathematical vulnerabilities in the
decision boundaries of
high-dimensional neural networks. As
Artificial Intelligence (AI) systems
become integral to safety-critical infrastructure, understanding how these vulnerabilities function is essential for
developing robust AI safety protocols and defense
mechanisms.
How Adversarial Attacks Work
In a typical deep learning (DL) training process,
a model optimizes its weights to minimize error on a training dataset. However, these models essentially create
complex maps in a multi-dimensional space. An adversarial attack calculates the precise "direction" in this
space needed to push an input across a boundary, flipping the model's classification. For instance, in
computer vision (CV), changing the pixel values
of a panda image by a calculated amount of "noise" might cause the system to confidently misclassify it as a
gibbon, even though the image still looks exactly like a panda to the human eye.
Attack strategies are generally categorized by the level of access the attacker has to the target system:
-
White-Box Attacks: The attacker
has full transparency into the model's architecture, gradients, and
model weights. This allows them to mathematically
compute the most effective perturbation, often using techniques like the Fast Gradient Sign Method (FGSM).
-
Black-Box Attacks:
The attacker has no knowledge of the internal model parameters and can only observe inputs and outputs. Attackers
often use a "substitute model" to generate adversarial examples that transfer effectively to the target
system, a property known as transferability.
Real-World Applications and Risks
While often discussed in theoretical research, adversarial attacks pose tangible risks to real-world deployments,
particularly in autonomous systems and security.
-
Autonomous Vehicles:
Self-driving cars rely heavily on
object detection to interpret traffic signs.
Research has demonstrated that applying carefully crafted stickers or tape to a stop sign can trick the vehicle's
vision system into perceiving it as a speed limit sign. This type of physical-world attack could lead to dangerous
failures in AI in automotive applications.
-
Facial Recognition Evaders:
Security systems that control access based on biometrics can be compromised by adversarial "patches."
These can be printed patterns worn on glasses or clothing that disrupt the
feature extraction process. This allows an
unauthorized individual to either evade detection entirely or impersonate a specific user, bypassing
security alarm systems.
Generating Adversarial Examples in Python
To understand how fragile some models can be, it is helpful to see how easily an image can be perturbed. While
standard inference with models like YOLO26 is robust for
general use, researchers often simulate attacks to improve
model monitoring and defense. The following
conceptual example uses PyTorch to show how gradients are used to calculate an adversarial perturbation (noise) for an
image.
import torch.nn.functional as F
# Assume 'model' is a loaded PyTorch model and 'image' is a normalized tensor
# 'target_class' is the correct label index for the image
def generate_adversarial_noise(model, image, target_class, epsilon=0.01):
# Enable gradient calculation for the input image
image.requires_grad = True
# Forward pass: get prediction
output = model(image)
# Calculate loss based on the correct class
loss = F.nll_loss(output, target_class)
# Backward pass: calculate gradients of loss w.r.t input
model.zero_grad()
loss.backward()
# Create perturbation using the sign of the data gradient (FGSM)
# This pushes the image in the direction of maximizing error
perturbation = epsilon * image.grad.data.sign()
return perturbation
Related Concepts
It is important to distinguish adversarial attacks from other forms of model failure or manipulation:
-
Data Poisoning:
Unlike adversarial attacks which manipulate the input during inference (testing time), data poisoning
involves corrupting the training data itself before
the model is built, embedding hidden backdoors or biases.
-
Prompt Injection: This is
specific to
Large Language Models (LLMs) and text
interfaces. While conceptually similar—tricking the model—it relies on semantic language manipulation rather than
mathematical perturbation of pixel or signal data.
-
Overfitting: This is a training
failure where a model learns noise in the training data rather than the underlying pattern. Overfitted models are
often more susceptible to adversarial attacks because their decision boundaries are overly complex and brittle.
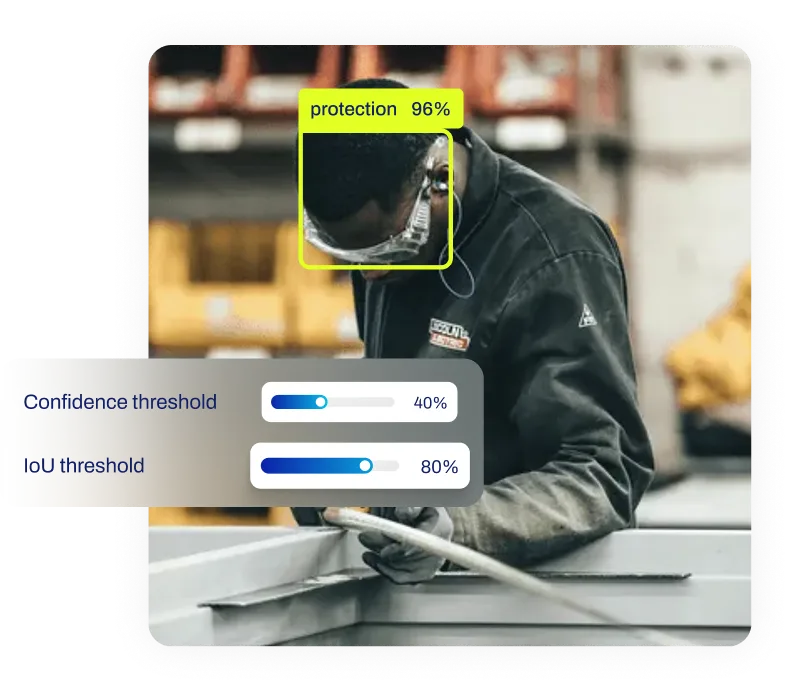
Developing defenses against these attacks is a core component of modern
MLOps. Techniques such as
adversarial training—where attacked examples are added to the training set—help models become more resilient.
Platforms like the Ultralytics Platform facilitate rigorous training
and validation pipelines, allowing teams to evaluate model robustness before deploying to edge devices.







.webp)