Data Security
Explore essential data security strategies for AI. Learn to protect Ultralytics YOLO26 models, defend against adversarial attacks, and implement automated redaction.
Data security encompasses the protective measures, strategies, and technologies employed to safeguard digital
information from unauthorized access, corruption, theft, or disruption throughout its lifecycle. In the context of
Machine Learning (ML) and
Artificial Intelligence (AI), this
discipline is paramount for ensuring the reliability of predictive systems and maintaining user trust. It involves
securing the vast datasets required for training, protecting the
proprietary algorithms that define model behavior, and hardening the infrastructure where these models operate. A
comprehensive security strategy addresses the "CIA triad"—ensuring
confidentiality, integrity, and availability
of data assets.
The Role of Security in AI Pipelines
As organizations increasingly integrate
computer vision (CV) and other AI technologies
into critical workflows, the attack surface for potential breaches expands. Securing an AI pipeline is distinct from
traditional IT security because the models themselves can be targeted or manipulated.
-
Intellectual Property Protection: State-of-the-art architectures, such as
YOLO26, represent significant investments in research and
computational resources. Robust security protocols, including
model encryption standards, are essential to prevent model extraction or theft
by competitors.
-
Defending Against Adversarial Attacks: Without adequate defenses,
neural networks are vulnerable to
adversarial attacks. In these scenarios,
malicious actors introduce subtle, often imperceptible, noise to input data to trick the model into making incorrect
classifications, which poses severe risks in safety-critical systems like autonomous driving.
-
Preventing Data Poisoning: Security measures must prevent "data poisoning," where
attackers inject malicious samples into the
training data to compromise the model's future
behavior. This is particularly critical for systems utilizing
active learning loops where the model
continuously updates based on new inputs. For a deeper dive into these threats, the
OWASP Machine Learning Security Top 10
provides an industry-standard framework.
Real-World Applications
Data security is a foundational requirement for deploying
trustworthy AI systems across sensitive
industries.
Healthcare Compliance and Anonymization
In the domain of AI in healthcare, handling
patient data requires strict adherence to regulations like HIPAA.
When hospitals employ
medical image analysis to detect tumors or
fractures, the data pipeline must be encrypted both at rest and in transit. Furthermore, systems often strip
DICOM metadata or utilize
Edge AI to process images locally on the device, ensuring
that sensitive Personally Identifiable Information (PII) never leaves the secure facility network.
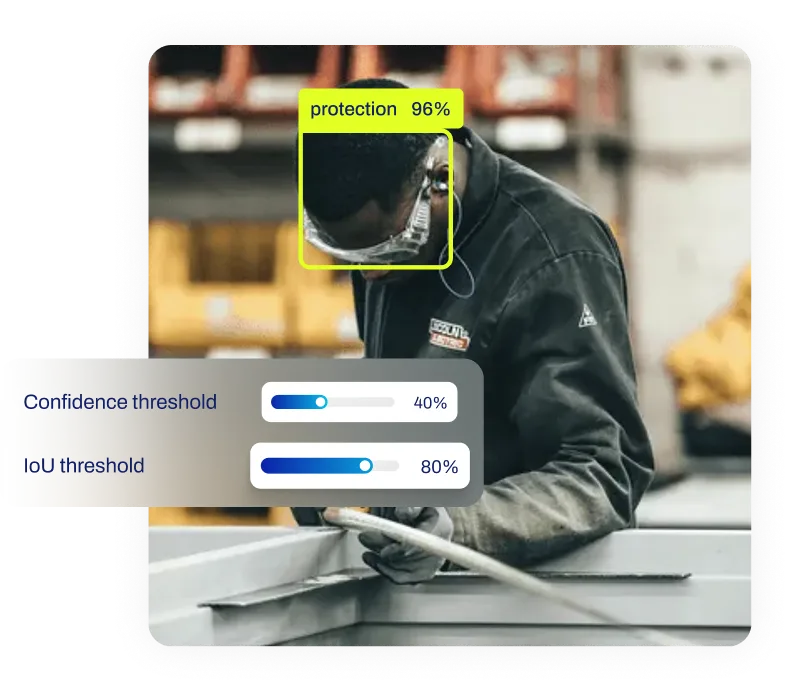
Smart City Surveillance
Modern Smart Cities rely on
object detection to manage traffic flow and
enhance public safety. To align with privacy standards like the GDPR, security cameras
often implement real-time redaction. This ensures that while the system can count vehicles or detect accidents, it
automatically obscures license plates and faces to protect citizen identities.
Technical Implementation: Automated Redaction
One common data security technique in computer vision is the automated blurring of sensitive objects during inference.
The following Python code demonstrates how to use ultralytics with the
YOLO26 model to detect persons in an image and apply a
Gaussian blur to their bounding boxes, effectively anonymizing the individuals before the data is stored or
transmitted.
import cv2
from ultralytics import YOLO
# Load the YOLO26 model (optimized for real-time inference)
model = YOLO("yolo26n.pt")
image = cv2.imread("street_scene.jpg")
# Perform object detection to find persons (class index 0)
results = model(image, classes=[0])
# Blur the detected regions to protect identity
for result in results:
for box in result.boxes.xyxy:
x1, y1, x2, y2 = map(int, box)
# Apply Gaussian blur to the Region of Interest (ROI)
image[y1:y2, x1:x2] = cv2.GaussianBlur(image[y1:y2, x1:x2], (51, 51), 0)
Data Security vs. Data Privacy
While frequently used interchangeably, it is crucial to distinguish between Data Security and
Data Privacy.
-
Data Security refers to the mechanisms and tools used to protect data from unauthorized
access or malicious attacks. This encompasses encryption, firewalls, and
access control lists (ACLs).
-
Data Privacy refers to the policies and legal rights governing how data is collected,
shared, and used. It focuses on user consent and ensuring data is used only for its intended purpose.
Security is the technical enabler of privacy; without robust security measures, privacy policies cannot be effectively
enforced. For teams managing the entire ML lifecycle, the
Ultralytics Platform offers a centralized environment to annotate,
train, and deploy models while maintaining rigorous security standards for dataset management.







.webp)